Search
Recent comments
- patriotism....
3 hours 8 min ago - belittling russia......
3 hours 36 min ago - Запад толкает Украину на последнюю битву....
3 hours 50 min ago - fourteen points....
3 hours 59 min ago - der philosophische glaube....
4 hours 10 min ago - seriously?...
4 hours 24 min ago - AfD....
4 hours 52 min ago - undesirables...
5 hours 8 min ago - assistant spies......
5 hours 33 min ago - brics.....
8 hours 41 min ago
Democracy Links
Member's Off-site Blogs
the spying business...
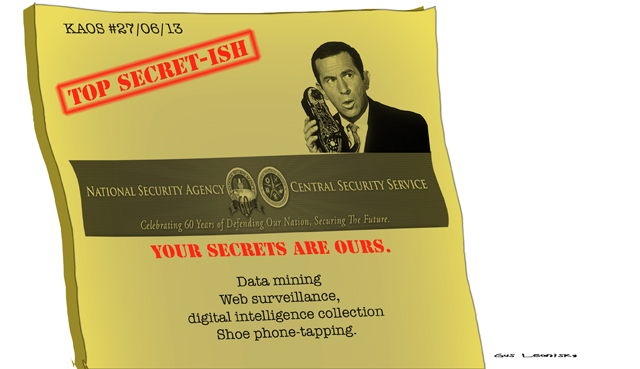
"Intelligence," Corporatism, and the Dance of Death
You may at first think the following is a bad joke, but I assure you it is not a joke at all. At the very end of this NYT story about Booz Allen and the complex interconnections between nominally "private" business and the national intelligence community, we read:
But the legal warnings at the end of its financial report offered a caution that the company could be hurt by “any issue that compromises our relationships with the U.S. government or damages our professional reputation."
By Friday, shares of Booz Allen had slid nearly 6 percent since the revelations.
And a new job posting appeared on its Web site for a systems administrator in Hawaii, “secret clearance required.”Yes, that appears to be Edward Snowden's old job.
Crappy spy fiction doesn't look quite so crappy now, does it? In many respects -- in fact, I would argue in every critical respect -- the spy business is actually that dumb.
In an earlier post about the NSA/surveillance stories, I discussed the profoundly offensive elitism involved in the argument that "special" people in both government and journalism, people endowed with understanding and judgment that is the envy of the gods and forever denied to all us ordinary schlubs, should decide what information will be provided to the motley mass of humans who merely pay for all of it, and for whose benefit all this godlike work is supposedly undertaken. Talk about idiocies: "We're doing all this for you! You're too stupid to be told most of what we're doing!" Put it on a bumper sticker, baby, so we can throw rotten eggs at it.
http://powerofnarrative.blogspot.co.uk/2013/06/intelligence-corporatism-and-dance-of.html
- By Gus Leonisky at 27 Jun 2013 - 10:03pm
- Gus Leonisky's blog
- Login or register to post comments
we will decide what you need to know...
Follow the Money: The Secret Heart of the Secret State
WRITTEN BY CHRIS FLOYD
TUESDAY, 18 JUNE 2013 23:53
No one, anywhere, has been writing about the deeper and wider implications of the Snowden revelations than Arthur Silber. (I hope you're not surprised by this.) In a series of powerful, insightful essays, Silber has, among other things, laid bare the dangers of the oddly circumscribed 'gatekeeper' approach of the journalistic guardians (at, ironically, the Guardian) of Snowden's secrets, particularly their slow drip-feed of carefully self-censored tidbits from the famous Powerpoint presentation that Snowden secreted from the bowels of the United Stasi of the American intelligent apparat. Eschewing the Wikileaks approach, the guardians at the Guardian have not let us judge the material for ourselves, opting instead to adopt, unwittingly, the same approach of the apparat: "we are the keepers of knowledge, we will decide what you need to know."
As Silber notes, this doesn't vitiate the worth of the revelations, but it does dilute their impact, leaving gaps that the apparat -- and its truly repulsive apologists all through the 'liberal media' -- can exploit to keep muddying the waters. He explores these ramifications, and others, in "In Praise of Mess, Chaos and Panic" and "Fed Up With All the Bullshit."
read more: http://www.chris-floyd.com/component/content/article/1-latest-news/2327-follow-the-money-the-secret-heart-of-the-secret-state.html
if god had a phone ....
In the course of his professional life in the world of national security Edward Snowden must have gone through numerous probing interviews, lie detector examinations, and exceedingly detailed background checks, as well as filling out endless forms carefully designed to catch any kind of falsehood or inconsistency.
The Washington Post (June 10) reported that “several officials said the CIA will now undoubtedly begin reviewing the process by which Snowden may have been hired, seeking to determine whether there were any missed signs that he might one day betray national secrets.”
Yes, there was a sign they missed – Edward Snowden had something inside him shaped like a conscience, just waiting for a cause.
It was the same with me. I went to work at the State Department, planning to become a Foreign Service Officer, with the best – the most patriotic – of intentions, going to do my best to slay the beast of the International Communist Conspiracy. But then the horror, on a daily basis, of what the United States was doing to the people of Vietnam was brought home to me in every form of media; it was making me sick at heart. My conscience had found its cause, and nothing that I could have been asked in a pre-employment interview would have alerted my interrogators of the possible danger I posed because I didn’t know of the danger myself. No questioning of my friends and relatives could have turned up the slightest hint of the radical anti-war activist I was to become. My friends and relatives were to be as surprised as I was to be. There was simply no way for the State Department security office to know that I should not be hired and given a Secret Clearance. 1
So what is a poor National Security State to do? Well, they might consider behaving themselves. Stop doing all the terrible things that grieve people like me and Edward Snowden and Bradley Manning and so many others. Stop the bombings, the invasions, the endless wars, the torture, the sanctions, the overthrows, the support of dictatorships, the unmitigated support of Israel; stop all the things that make the United States so hated, that create all the anti-American terrorists, that compel the National Security State – in pure self defense – to spy on the entire world.
Eavesdropping on the planet
The above is the title of an essay that I wrote in 2000 that appeared as a chapter in my book Rogue State: A Guide to the World’s Only Superpower. Here are some excerpts that may help to put the current revelations surrounding Edward Snowden into perspective …
Can people in the 21st century imagine a greater invasion of privacy on all of earth, in all of history? If so, they merely have to wait for technology to catch up with their imagination.
Like a mammoth vacuum cleaner in the sky, the National Security Agency (NSA) sucks it all up: home phone, office phone, cellular phone, email, fax, telex … satellite transmissions, fiber-optic communications traffic, microwave links … voice, text, images … captured by satellites continuously orbiting the earth, then processed by high-powered computers … if it runs on electromagnetic energy, NSA is there, with high tech. Twenty-four hours a day. Perhaps billions of messages sucked up each day. No one escapes. Not presidents, prime ministers, the UN Secretary-General, the pope, the Queen of England, embassies, transnational corporation CEOs, friend, foe, your Aunt Lena … if God has a phone, it’s being monitored … maybe your dog isn’t being tapped. The oceans will not protect you. American submarines have been attaching tapping pods to deep underwater cables for decades.
Under a system codenamed ECHELON, launched in the 1970s, the NSA and its junior partners in Britain, Australia, New Zealand, and Canada operate a network of massive, highly automated interception stations, covering the globe amongst them. Any of the partners can ask any of the others to intercept its own domestic communications. It can then truthfully say it does not spy on its own citizens.
Apart from specifically-targeted individuals and institutions, the ECHELON system works by indiscriminately intercepting huge quantities of communications and using computers to identify and extract messages of interest from the mass of unwanted ones. Every intercepted message – all the embassy cables, the business deals, the sex talk, the birthday greetings – is searched for keywords, which could be anything the searchers think might be of interest. All it takes to flag a communication is for one of the parties to use a couple or so of the key words in the ECHELON “dictionary” – “He lives in a lovely old white house on Bush Street, right near me. I can shoot over there in two minutes.” Within limitations, computers can “listen” to telephone calls and recognize when keywords are spoken. Those calls are extracted and recorded separately, to be listened to in full by humans. The list of specific targets at any given time is undoubtedly wide ranging, at one point including the likes of Amnesty International and Christian Aid.
ECHELON is carried out without official acknowledgment of its existence, let alone any democratic oversight or public or legislative debate as to whether it serves a decent purpose. The extensiveness of the ECHELON global network is a product of decades of intense Cold War activity. Yet with the end of the Cold War, its budget – far from being greatly reduced – was increased, and the network has grown in both power and reach; yet another piece of evidence that the Cold War was not a battle against something called “the international communist conspiracy”.
The European Parliament in the late 1990s began to wake up to this intrusion into the continent’s affairs. The parliament’s Civil Liberties Committee commissioned a report, which appeared in 1998 and recommended a variety of measures for dealing with the increasing power of the technologies of surveillance. It bluntly advised: “The European Parliament should reject proposals from the United States for making private messages via the global communications network [Internet] accessible to US intelligence agencies.” The report denounced Britain’s role as a double-agent, spying on its own European partners.
Despite these concerns the US has continued to expand ECHELON surveillance in Europe, partly because of heightened interest in commercial espionage – to uncover industrial information that would provide American corporations with an advantage over foreign rivals.
German security experts discovered several years ago that ECHELON was engaged in heavy commercial spying in Europe. Victims included such German firms as the wind generator manufacturer Enercon. In 1998, Enercon developed what it thought was a secret invention, enabling it to generate electricity from wind power at a far cheaper rate than before. However, when the company tried to market its invention in the United States, it was confronted by its American rival, Kenetech, which announced that it had already patented a near-identical development. Kenetech then brought a court order against Enercon to ban the sale of its equipment in the US. In a rare public disclosure, an NSA employee, who refused to be named, agreed to appear in silhouette on German television to reveal how he had stolen Enercon’s secrets by tapping the telephone and computer link lines that ran between Enercon’s research laboratory and its production unit some 12 miles away. Detailed plans of the company’s invention were then passed on to Kenetech.
In 1994, Thomson S.A., located in Paris, and Airbus Industrie, based in Blagnac Cedex, France, also lost lucrative contracts, snatched away by American rivals aided by information covertly collected by NSA and CIA. The same agencies also eavesdropped on Japanese representatives during negotiations with the United States in 1995 over auto parts trade.
German industry has complained that it is in a particularly vulnerable position because the government forbids its security services from conducting similar industrial espionage. “German politicians still support the rather naive idea that political allies should not spy on each other’s businesses. The Americans and the British do not have such illusions,” said journalist Udo Ulfkotte, a specialist in European industrial espionage, in 1999.
That same year, Germany demanded that the United States recall three CIA operatives for their activities in Germany involving economic espionage. The news report stated that the Germans “have long been suspicious of the eavesdropping capabilities of the enormous U.S. radar and communications complex at Bad Aibling, near Munich”, which is in fact an NSA intercept station. “The Americans tell us it is used solely to monitor communications by potential enemies, but how can we be entirely sure that they are not picking up pieces of information that we think should remain completely secret?” asked a senior German official. Japanese officials most likely have been told a similar story by Washington about the more than a dozen signals intelligence bases that Japan has allowed to be located on its territory.
In their quest to gain access to more and more private information, the NSA, the FBI, and other components of the US national security establishment have been engaged for years in a campaign to require American telecommunications manufacturers and carriers to design their equipment and networks to optimize the authorities’ wiretapping ability. Some industry insiders say they believe that some US machines approved for export contain NSA “back doors” (also called “trap doors”).
The United States has been trying to persuade European Union countries as well to allow it “back-door” access to encryption programs, claiming that this was to serve the needs of law-enforcement agencies. However, a report released by the European Parliament in May 1999 asserted that Washington’s plans for controlling encryption software in Europe had nothing to do with law enforcement and everything to do with US industrial espionage. The NSA has also dispatched FBI agents on break-in missions to snatch code books from foreign facilities in the United States, and CIA officers to recruit foreign communications clerks abroad and buy their code secrets, according to veteran intelligence officials.
For decades, beginning in the 1950s, the Swiss company Crypto AG sold the world’s most sophisticated and secure encryption technology. The firm staked its reputation and the security concerns of its clients on its neutrality in the Cold War or any other war. The purchasing nations, some 120 of them – including prime US intelligence targets such as Iran, Iraq, Libya and Yugoslavia – confident that their communications were protected, sent messages from their capitals to their embassies, military missions, trade offices, and espionage dens around the world, via telex, radio, and fax. And all the while, because of a secret agreement between the company and NSA, these governments might as well have been hand delivering the messages to Washington, uncoded. For their Crypto AG machines had been rigged before being sold to them, so that when they used them the random encryption key could be automatically and clandestinely transmitted along with the enciphered message. NSA analysts could read the messages as easily as they could the morning newspaper.
In 1986, because of US public statements concerning the La Belle disco bombing in West Berlin, the Libyans began to suspect that something was rotten with Crypto AG’s machines and switched to another Swiss firm, Gretag Data Systems AG. But it appears that NSA had that base covered as well. In 1992, after a series of suspicious circumstances over the previous few years, Iran came to a conclusion similar to Libya’s, and arrested a Crypto AG employee who was in Iran on a business trip. He was eventually ransomed, but the incident became well known and the scam began to unravel in earnest.
In September 1999 it was revealed that NSA had arranged with Microsoft to insert special “keys” into Windows software, in all versions from 95-OSR2 onwards. An American computer scientist, Andrew Fernandez of Cryptonym in North Carolina, had disassembled parts of the Windows instruction code and found the smoking gun – Microsoft’s developers had failed to remove the debugging symbols used to test this software before they released it. Inside the code were the labels for two keys. One was called “KEY”. The other was called “NSAKEY”. Fernandez presented his finding at a conference at which some Windows developers were also in attendance. The developers did not deny that the NSA key was built into their software, but they refused to talk about what the key did, or why it had been put there without users’ knowledge. Fernandez says that NSA’s “back door” in the world’s most commonly used operating system makes it “orders of magnitude easier for the US government to access your computer.”
In February 2000, it was disclosed that the Strategic Affairs Delegation (DAS), the intelligence arm of the French Defense Ministry, had prepared a report in 1999 which also asserted that NSA had helped to install secret programs in Microsoft software. According to the DAS report, “it would seem that the creation of Microsoft was largely supported, not least financially, by the NSA, and that IBM was made to accept the [Microsoft] MS-DOS operating system by the same administration.” The report stated that there had been a “strong suspicion of a lack of security fed by insistent rumors about the existence of spy programs on Microsoft, and by the presence of NSA personnel in Bill Gates’ development teams.” The Pentagon, said the report, was Microsoft’s biggest client in the world.
Recent years have seen disclosures that in the countdown to their invasion of Iraq in 2003, the United States had listened in on UN Secretary-General Kofi Annan, UN weapons inspectors in Iraq, and all the members of the UN Security Council during a period when they were deliberating about what action to take in Iraq.
It’s as if the American national security establishment feels that it has an inalienable right to listen in; as if there had been a constitutional amendment, applicable to the entire world, stating that “Congress shall make no law abridging the freedom of the government to intercept the personal communications of anyone.” And the Fourth Amendment had been changed to read: “Persons shall be secure in their persons, houses, papers, and effects, against unreasonable searches and seizures, except in cases of national security, real or alleged.” 2
The leading whistleblower of all time: Philip Agee
Before there was Edward Snowden, William Binney and Thomas Drake … before there was Bradley Manning, Sibel Edmonds and Jesselyn Radack … there was Philip Agee. What Agee revealed is still the most startling and important information about US foreign policy that any American government whistleblower has ever revealed.
Philip Agee spent 12 years (1957-69) as a CIA case officer, most of it in Latin America. His first book, Inside the Company: CIA Diary, published in 1974 – a pioneering work on the Agency’s methods and their devastating consequences – appeared in about 30 languages around the world and was a best seller in many countries; it included a 23-page appendix with the names of hundreds of undercover Agency operatives and organizations.
Under CIA manipulation, direction and, usually, their payroll, were past and present presidents of Mexico, Colombia, Uruguay, and Costa Rica, “our minister of labor”, “our vice-president”, “my police”, journalists, labor leaders, student leaders, diplomats, and many others. If the Agency wished to disseminate anti-communist propaganda, cause dissension in leftist ranks, or have Communist embassy personnel expelled, it need only prepare some phoney documents, present them to the appropriate government ministers and journalists, and – presto! – instant scandal.
Agee’s goal in naming all these individuals, quite simply, was to make it as difficult as he could for the CIA to continue doing its dirty work.
A common Agency tactic was writing editorials and phoney news stories to be knowingly published by Latin American media with no indication of the CIA authorship or CIA payment to the media. The propaganda value of such a “news” item might be multiplied by being picked up by other CIA stations in Latin America who would disseminate it through a CIA-owned news agency or a CIA-owned radio station. Some of these stories made their way back to the United States to be read or heard by unknowing North Americans.
Wooing the working class came in for special treatment. Labor organizations by the dozen, sometimes hardly more than names on stationery, were created, altered, combined, liquidated, and new ones created again, in an almost frenzied attempt to find the right combination to compete with existing left-oriented unions and take national leadership away from them.
In 1975 these revelations were new and shocking; for many readers it was the first hint that American foreign policy was not quite what their high-school textbooks had told them nor what theNew York Times had reported.
“As complete an account of spy work as is likely to be published anywhere, an authentic account of how an ordinary American or British ‘case officer’ operates … All of it … presented with deadly accuracy,” wrote Miles Copeland, a former CIA station chief, and ardent foe of Agee. (There’s no former CIA officer more hated by members of the intelligence establishment than Agee; no one’s even close; due in part to his travelling to Cuba and having long-term contact with Cuban intelligence.)
In contrast to Agee, WikiLeaks withheld the names of hundreds of informants from the nearly 400,000 Iraq war documents it released.
In 1969, Agee resigned from the CIA (and colleagues who “long ago ceased to believe in what they are doing”).
While on the run from the CIA as he was writing Inside the Company – at times literally running for his life – Agee was expelled from, or refused admittance to, Italy, Britain, France, West Germany, the Netherlands, and Norway. (West Germany eventually gave him asylum because his wife was a leading ballerina in the country.) Agee’s account of his period on the run can be found detailed in his book On the Run (1987). It’s an exciting read.
Notes
To read about my State Department and other adventures, see my book West-Bloc Dissident: A Cold war Memoir (2002) ↩
See Rogue State: A Guide to the World’s Only Superpower, chapter 21, for the notes for the above. ↩
Any part of this report may be disseminated without permission, provided attribution to William Blum as author and a link to this website are given.
The Anti-Empire Report
slack with security clearance checks...
Company allegedly misled government about security clearance checks
By Tom Hamburger and Zachary A. Goldfarb, Friday, June 28, 11:17 AMFederal investigators have told lawmakers they have evidence that USIS, the contractor that screened Edward Snowden for his top-secret clearance, repeatedly misled the government about the thoroughness of its background checks, according to people familiar with the matter.
The alleged transgressions are so serious that a federal watchdog indicated he plans to recommend that the Office of Personnel Management, which oversees most background checks, end ties with USIS unless it can show it is performing responsibly, the people said.
Cutting off USIS could present a major logistical quagmire for the nation’s already-jammed security clearance process. The federal government relies heavily on contractors to approve workers for some of its most sensitive jobs in defense and intelligence. Falls Church-based USIS is the largest single private provider for government background checks.
The inspector general of OPM, working with the Justice Department, is examining whether USIS failed to meet a contractual obligation that it would conduct reviews of all background checks the company performed on behalf of government agencies, the people familiar with the matter said, speaking on the condition of anonymity because the investigation has not yet been resolved.
After conducting an initial background check of a candidate for employment, USIS was required to perform a second review to make sure no important details had been missed. From 2008 through 2011, USIS allegedly skipped this second review in up to 50 percent of the cases. But it conveyed to federal officials that these reviews had, in fact, been performed.
http://www.washingtonpost.com/business/economy/company-allegedly-misled-government-about-security-clearance-checks/2013/06/27/dfb7ee04-df5c-11e2-b2d4-ea6d8f477a01_print.html
cyber olympic games...
Justice Dept. targets general in leak probe
By Greg Miller and Sari Horwitz, Friday, June 28, 10:47 AMA retired four-star Marine Corps general who served as the nation’s second-ranking military officer is a target of a Justice Department investigation into a leak of information about a covert U.S.-Israeli cyberattack on Iran’s nuclear program, a senior Obama administration official said.
Retired Gen. James E. “Hoss” Cartwright served as deputy chairman of the Joint Chiefs of Staff and was part of President Obama’s inner circle on a range of critical national security issues before he retired in 2011.
The administration official said that Cartwright is suspected of revealing information about a highly classified effort to use a computer virus later dubbed Stuxnet to sabotage equipment in Iranian nuclear enrichment plants.
Stuxnet was part of a broader cyber campaign called Olympic Games that was disclosed by the New York Times last year as one of the first major efforts by the United States to use computer code as a destructive weapon against a key adversary.
Cartwright, who helped launch that campaign under President Bush and pushed for its escalation under Obama, was recently informed that he was a “target” of a wide-ranging Justice Department probe into the leak, according to the senior official, who spoke on the condition of anonymity because the investigation is ongoing.
Justice Department officials declined to comment on the case, as did Marcia Murphy, a spokeswoman for the U.S. attorney’s office in Maryland, which is in charge of the investigation.
Neither Cartwright nor his attorney, former White House counsel Greg Craig, responded to requests for comment.
The revelation, which was first reported by NBC News, means that an administration that has already launched more leaks prosecutions than all of its predecessors combined is now focused on one of its own. Since Obama took office, the Justice Department has prosecuted or charged eight people for alleged violations of the Espionage Act.
http://www.washingtonpost.com/world/national-security/justice-dept-targets-general-in-leak-probe/2013/06/27/9ad8bc4e-df7c-11e2-b2d4-ea6d8f477a01_print.html
repeat of comment somewhere else:
Gus: Let me see, people didnot know they were being spied upon? Especially after a few years' warning for the telcos to keep their data for so long?... If one is going to commit a bad deed, one is not going to make waves, including communicate via the mass electronic networks, is one? There are still old-fashioned ways to network without being noticed... Including good old fashioned encoding and speed air-wave transmissions in short bursts at irregular intervals...
Meanwhile the spying on the American public as well as spying upon other countries by tapping into their networks — including that of a scientific university in Hong Kong with probably the ulterior motive of stealing scientific information — is rather duplicitous... Mind you as I have mentioned in the comments above, all countries do it, including for industrial espionage... In all this I have a feeling that "spying against terrorism" has become a lowly ranked purpose... And this is most likely why the Yanks hate being in the open...
Meanwhile, the NSA makes Uncle Rupe smell like roses (with thorns, of course)...
network hygiene...
US army blocks access to Guardian website to preserve 'network hygiene'
Military admits to filtering reports and content relating to government surveillance programs for thousands of personnelThe US army has admitted to blocking access to parts of the Guardian website for thousands of defence personnel across the country.
A spokesman said the military was filtering out reports and content relating to government surveillance programs to preserve "network hygiene" and prevent any classified material appearing on unclassified parts of its computer systems.
The confirmation follows reports in the Monterey Herald that staff at the Presidio military base south of San Francisco had complained of not being able to access the Guardian's UK site at all, and had only partial access to the US site, following publication of leaks from whistleblower Edward Snowden.
The Pentagon insisted the Department of Defense was not seeking to block the whole website, merely taking steps to restrict access to certain content.
http://www.guardian.co.uk/world/2013/jun/28/us-army-blocks-guardian-website-access/print
Did the US Army get advice from the Chinese on how to?...
spies and spiegel...
NSA Spied on European Union Offices
By Laura Poitras, Marcel Rosenbach, Fidelius Schmid and Holger Stark
America's NSA intelligence service allegedly targeted the European Union with its spying activities. According to SPIEGEL information, the US placed bugs in the EU representation in Washington and infiltrated its computer network. Cyber attacks were also perpetrated against Brussels in New York and Washington.
Information obtained by SPIEGEL shows that America's National Security Agency (NSA) not only conducted online surveillance of European citizens, but also appears to have specifically targeted buildings housing European Union institutions. The information appears in secret documents obtained by whistleblower Edward Snowden that SPIEGEL has in part seen. A "top secret" 2010 document describes how the secret service attacked the EU's diplomatic representation in Washington.
The document suggests that in addition to installing bugs in the building in downtown Washington, DC, the European Union representation's computer network was also infiltrated. In this way, the Americans were able to access discussions in EU rooms as well as emails and internal documents on computers.
The attacks on EU institutions show yet another level in the broad scope of the NSA's spying activities. For weeks now, new details about Prism and other surveillance programs have been emerging from what had been compiled by whistleblower Snowden. It has also been revealed that the British intelligence service GCHQ operates a similar program under the name Tempora with which global telephone and Internet connections are monitored.
The documents SPIEGEL has seen indicate that the EU representation to the United Nations was attacked in a manner similar to the way surveillance was conducted against its offices in Washington. An NSA document dated September 2010 explicitly names the Europeans as a "location target".
The documents also indicate the US intelligence service was responsible for an electronic eavesdropping operation in Brussels. A little over five years ago, EU security experts noticed several telephone calls that were apparently targeting the remote maintenance system in the Justus Lipsius Building, where the EU Council of Ministers and the European Council are located. The calls were made to numbers that were very similar to the one used for the remote administration of the building's telephone system.
Security officials managed to track the calls to NATO headquarters in the Brussels suburb of Evere. A precise analysis showed that the attacks on the telecommunications system had originated from a building complex separated from the rest of the NATO headquarters that is used by NSA experts.
A review of the remote maintenance system showed that it had been called and reached several times from precisely that NATO complex. Every EU member state has rooms in the Justus Lipsius Building that can be used by EU ministers. They also have telephone and Internet connections at their disposal.
http://www.spiegel.de/international/europe/nsa-spied-on-european-union-offices-a-908590.html
for those who don't know my views...
Washington’s efforts to contain fallout from the Snowden espionage debacle unravelled dramatically on Sunday as the European Union and individual European governments nations were revealed as targets of industrial-scale American snooping into government and private communications around the globe.Suggesting that the leaker, former contract intelligence worker Edward Snowden, has put in place an elaborate country-by-country plan of leaks to cause maximum diplomatic embarrassment for the US, the German magazine Der Spiegel published the first in what is says is a series of reports, causing near-apoplexy in the capitals of the continent.
Such behavior among allies is intolerable. They have completely lost balance – George Orwell is nothing by comparison.
Elmar Brok, chairman of the EU foreign affairs committeeAccording to the Der Spiegel reports, The US National Security Agency has bugged the EU offices in Washington and its mission to the United Nations in New York and has hacked into the EU’s computer network, directing a flood of EU correspondence, documentation and high-level meeting conversations to analysts in the US.Also revealed is a huge eavesdropping operation in Brussels, seemingly conducted from a building at the headquarters of NATO, of which 20 or more European countries are members, against on the telecommunications system at the EU headquarters in the same city. According to the reports, every EU member state has rooms at the building, with telephone and internet connections, which are used by EU ministers.
Singled out for the greatest US attention, in what appeared to be an operation that goes beyond that focused on the EU, is Germany with as many as 500 million communications, by phone and internet, being monitored each month, according to the documents.
“We can attack the signals of most foreign and third-class partners, and we do it too,” the German magazine quotes from one of the NSA documents.
Read more: http://www.smh.com.au/technology/technology-news/eu-enraged-as-snowden-reveals-evidence-of-mass-hacking-by-us-20130701-2p5v7.html#ixzz2XkRUmUYB
Persons who are familiar with my views would know by now that I have exposed the "concept" that the USA has been trying very hard to make sure Europe was not "rising" economically... At every turn of US foreign policies there was a matey matey front but a divisive attitude below this smiling face. The US has been trying hard to undo the Germany-France relations by regularly making some offers to only one government while poopooing the other... The divide and conquer tactic has also been promoted by the US strong alliance with the UK (as seen during the Iraq war) — an alliance which has been designed to undermine Europe, while the UK is still holding to the pound sterling... The wonky banking system of the USA was underhandedly used to pollute the European banking system which for all intent and purposes is far more regulated than in the US. The way the US banks corrupted the Greek government to take some extra secret loans, not sanctioned by the EU was simply part of the plan to weaken Europe...
If one knows history this is not new... Under the generous cover of giving needed assistance to devastated Europe after WWII, the US started to control the dynamics of political influences in Europe. From the Marshall plan, then the Mutual Security Pact, Europe became dependant of the US. It was not charity but cheap loans that eventually had to be repaid — and until, such repayment, the US forces would stay in Europe... It was hard though for Europe to regain its feet... Germany had been devastated and conquered, France was divided and flattened in parts, and England was exhausted... Spain, still in the throes of Franco, was not part of the schemes.
The Cold War was being frothed up between the US and the USSR with Europe caught in the middle of the playground... Hope of survival was minimal and this made it difficult to have a grip on the future... Gloom was driving everything.
It was in 1963 that when the French and the Germans made a friendship pact, and in 1964 when France got out of NATO after having repaid all the debt to the US that the US got the wind up... Europe was starting to become "united"... Pound for pound, person for person, Europe as an entity could be as formidable as the USA. The USA does not want this to happen...
Gus
access denied...
The world's biggest investment banks colluded to stop competition in a profitable derivatives business according to EU authorities.
Between 2006 and 2009 Deutsche Borse and the Chicago Mercantile Exchange tried to enter the credit derivatives business, but were denied licences to offer trading in the products.
EU competition officials say that big banks were behind that refusal.
If the exchanges had been successful, banks may have lost out on business.
The report focuses on one particular financial product, the credit default swap (CDS), which is dominated by "over-the-counter" trading - trading provided directly by the big banks, instead of via a financial exchange.
CDS are used by companies and investors to protect themselves against potential losses from a debt going bad, or to speculate on the probability of a company or government going bust.
They were much talked about during the European debt crisis when bailouts caused steep losses for holders of Greek debt.
They were also accused of helping to propagate the 2008 financial crisis, particular when the large insurance company AIG, a major writer of CDS contracts, almost went bust.
Following the financial crisis, regulators in the US and Europe have been seeking to move trading of derivatives onto exchanges in order to reduce the risk of counterparties failing to pay out, and to increase transparency.
Unacceptable
http://www.bbc.co.uk/news/business-23128361
Read article above...
snowden on "violating global privacy"...
Interviewer: What is the mission of America's National Security Agency (NSA) -- and how is the job it does compatible with the rule of law?
Snowden: They're tasked to know everything of importance that happens outside of the United States. That's a significant challenge. When it is made to appear as though not knowing everything about everyone is an existential crisis, then you feel that bending the rules is okay. Once people hate you for bending those rules, breaking them becomes a matter of survival.
Interviewer: Are German authorities or German politicians involved in the NSA surveillance system?
Snowden: Yes, of course. "We"'re 1 in bed together with the Germans the same as with most other Western countries. For example, "we" 2 tip them off when someone we want is flying through their airports (that we for example, have learned from the cell phone of a suspected hacker's girlfriend in a totally unrelated third country -- and they hand them over to us. They 3 don't ask to justify how we know something, and vice versa, to insulate their political leaders from the backlash of knowing how grievously they're violating global privacy.
Interviewer: But if details about this system are now exposed, who will be charged?
Snowden: In front of US courts? I'm not sure if you're serious. An investigation found the specific people who authorized the warrantless wiretapping of millions and millions of communications, which per count would have resulted in the longest sentences in world history, and our highest official simply demanded the investigation be halted. Who "can" be brought up on charges is immaterial when the rule of law is not respected. Laws are meant for you, not for them.
read more: http://www.spiegel.de/international/world/interview-with-whistleblower-edward-snowden-on-global-spying-a-910006.html
no IBM data keys nor IBM backdoors in NSA spying...
Big Blue calls for a "robust debate on surveillance reforms" and says "governments must act to restore trust." It's the latest tech company to try to distance itself from the controversial spying program
by TaboolaTechnology giant IBM hasn’t given the U.S. National Security Agency access to any client data and would challenge any surveillance-related gag orders imposed by the government, a top company executive wrote in an open letter to clients Friday. The world’s largest technology services company also says it hasn’t put “backdoors” in any of its products or provided the NSA with encryption keys that would allow the agency to access client data, according to Robert C. Weber, IBM General Counsel and Senior Vice President for legal and regulatory affairs.
IBM’s letter, which is clearly designed to reassure clients who have been spooked by recent revelations about the role of major technology companies in U.S. surveillance programs, is Big Blue’s most detailed public statement following disclosures supplied by former NSA contractor Edward Snowden. Industry experts estimate that the NSA revelations could cost top U.S. tech companies billions of dollars over the next several years if international clients take their business elsewhere. Over half of IBM’s revenue comes from clients outside the U.S.
http://time.com/25410/ibm-nsa-letter/
I don't know but I would suspect that the NSA is using IBM mainframes to compile its data... But this does not mean that the IBM clients are not firewalled against the spying... Most likely the IBM company has not supplied ANY INFORMATION but the NSA may have ways to by-pass any firewalls... Who knows...
Read all articles from below the toon at top... Thanks.
not only they spy, they also manufacture fake information...
The White House confirms a US government aid agency was behind a text-message service that was allegedly designed to foment unrest in Cuba.
ZunZuneo, dubbed a "Cuban Twitter", had 40,000 subscribers at its height in a country with limited web access, reports the Associated Press.
The project is said to have lasted from 2009-12 when the grant money ran out.
The US reportedly hid its links to the network through shell firms and by routing messages via other countries.
There has been no official Cuban government reaction to the story.
'Bogus advertisements'The BBC's Sarah Rainsford in the Cuban capital of Havana says there is a thirst for information on the island, which has no independent media.
read more: http://www.bbc.com/news/world-us-canada-26876801
the NSA tampers with US-made internet routers...
Glenn Greenwald: how the NSA tampers with US-made internet routers
The NSA has been covertly implanting interception tools in US servers heading overseas – even though the US government has warned against using Chinese technology for the same reasons, says Glenn Greenwald, in an extract from his new book about the Snowden affair, No Place to HideThe drumbeat of American accusations against Chinese internet device manufacturers was unrelenting. In 2012, for example, a report from the House Intelligence Committee, headed by Mike Rogers, claimed that Huawei and ZTE, the top two Chinese telecommunications equipment companies, "may be violating United States laws" and have "not followed United States legal obligations or international standards of business behaviour". The committee recommended that "the United States should view with suspicion the continued penetration of the US telecommunications market by Chinese telecommunications companies".
The Rogers committee voiced fears that the two companies were enabling Chinese state surveillance, although it acknowledged that it had obtained no actual evidence that the firms had implanted their routers and other systems with surveillance devices. Nonetheless, it cited the failure of those companies to cooperate and urged US firms to avoid purchasing their products: "Private-sector entities in the United States are strongly encouraged to consider the long-term security risks associated with doing business with either ZTE or Huawei for equipment or services. US network providers and systems developers are strongly encouraged to seek other vendors for their projects. Based on available classified and unclassified information, Huawei and ZTE cannot be trusted to be free of foreign state influence and thus pose a security threat to the United States and to our systems."
The constant accusations became such a burden that Ren Zhengfei, the 69-year-old founder and CEO of Huawei, announced in November 2013 that the company was abandoning the US market. As Foreign Policy reported, Zhengfei told a French newspaper: "'If Huawei gets in the middle of US-China relations,' and causes problems, 'it's not worth it'."
But while American companies were being warned away from supposedly untrustworthy Chinese routers, foreign organisations would have been well advised to beware of American-made ones. A June 2010 report from the head of the NSA's Access and Target Development department is shockingly explicit. The NSA routinely receives – or intercepts – routers, servers and other computer network devices being exported from the US before they are delivered to the international customers.
The agency then implants backdoor surveillance tools, repackages the devices with a factory seal and sends them on. The NSA thus gains access to entire networks and all their users. The document gleefully observes that some "SIGINT tradecraft … is very hands-on (literally!)".
Read more: http://www.theguardian.com/books/2014/may/12/glenn-greenwald-nsa-tampers-us-internet-routers-snowden
allo? hello?... hallo?... ¡Hola?... kaixo?... aлло?... sveiki?
Germany's biggest telecoms company is to follow Vodafone in disclosing for the first time the number of surveillance requests it receives from governments around the world.
Deutsche Telekom, which owns half of Britain's EE mobile network and operates in 14 countries including the US, Spain and Poland, has already published surveillance data for its home nation – one of the countries that have reacted most angrily to the Edward Snowden revelations. In the wake of Vodafone's disclosures, first published in the Guardian on Friday, it announced that it would extend its disclosures to every other market where it operates and where it is legal.
A spokeswoman for Deutsche Telekom, which has 140 million customers worldwide, said: "Deutsche Telekom has initially focused on Germany when it comes to disclosure of government requests. We are currently checking if and to what extent our national companies can disclose information. We intend to publish something similar to Vodafone."
Bosses of the world's biggest mobile networks, many of which have headquarters in Europe, are gathering for an industry conference in Shanghai this weekend, and the debate is expected to centre on whether they should join Deutsche and Vodafone in using transparency to push back against the use of their technology for government surveillance.
Mobile companies, unlike social networks, cannot operate without a government-issued licence, and have previously been reluctant to discuss the extent of their cooperation with national security and law enforcement agencies.
But Vodafone broke cover on Friday by confirming that in around half a dozen of the markets in which it operates, governments in Europe and outside have installed their own secret listening equipment on its network and those of other operators.
read more: http://www.theguardian.com/world/2014/jun/06/deutsche-telekom-to-also-reveal-surveillance-data
See toon and story at top...
misawa spies...
New papers released by whistleblower Edward Snowden, and published by The Intercept, reveal that Japan made secret deals with the NSA – with one document noting that the agency's relationship with Tokyo goes back to the 1950s.
The information, published in collaboration with Japanese news outlet NHK on Monday, states that Japan has allowed the US National Security Agency (NSA) to maintain at least three bases on its territory while contributing more than half a billion dollars to help fund its facilities and operations.
In return, the NSA has provided Japanese spies with state-of-the-art surveillance tools and shared intelligence.
The Intercept notes multiple documents and instances which outline the NSA's ongoing relationship with the NSA.
However, it also notes that the agency has secretly spied on Japanese officials and institutions while maintaining friendly ties with Tokyo.
Back to the 1950sAccording to documents cited by The Intercept, the relationship between the NSA and Tokyo began in the 1950s, when the US continued to maintain a large presence in Japan despite the country's sovereignty being restored after years of US military occupation following World War II.
A document from 2007 shows that the NSA's presence in Japan was managed out of a "cover office" in the Minato area of downtown Tokyo for many years, within a US military compound called the Hardy Barracks.
It was from that office that the agency apparently maintained close relations with Japan's Directorate for Signals Intelligence (SIGINT).
But by 2007, the agency's low profile had ended, with the NSA determining that "cover operations are no longer required." It then relocated its main office in Japan to the US embassy in Tokyo.
“NSA’s partnership with Japan continues to grow in importance,” the agency wrote in a classified October 2007 report, adding that it planned to take the country “to the next level as an intelligence partner with the US."
Bump in the roadNews reports from September 1983 were dominated by the downing of Korean Airlines Flight 007, which was shot down by the Soviet Union after entering Soviet airspace.
But the case involved more than South Korea and the Soviet Union, with Tokyo and Washington engaged in a 'behind-closed-doors' dispute on secret surveillance related to the incident.
It came down to Japanese tapes which included intercepted conversations that proved the Soviet military was behind the attack. Washington wanted to obtain copies of the footage, but had to first seek approval from the head of the Japanese surveillance organization known as "G2 Annex."
Tokyo eventually signed off on the release, agreeing to send copies of the tapes to Washington.
From there, the footage was sent to New York City, where US Ambassador Jeane Kirkpatrick brought them to the United Nations headquarters.
While attending a meeting of the UN Security Council, Kirkpatrick slammed the Soviet Union for telling "lies, half lies, and excuses" about its involvement in the downing of the plane, stating that the evidence had been presented "in cooperation with the government of Japan."
The nod to Tokyo was not appreciated by the Japanese government, as the simple statement had exposed its spying capabilities.
The G2 Annex was then given orders limiting its cooperation with the US, which affected the NSA's relationship with its Japanese counterparts for almost a decade, at least until the Cold War ended in the early 1990s.
MisawaHowever, the relationship between the NSA and Tokyo was eventually mended. The agency now has a presence at several facilities in Japan – the most important of which is located at a large US airbase in Misawa, located about 400 miles north of Tokyo.
read more:
https://www.rt.com/news/386016-snowden-intercept-nsa-japan/
See toon at top...
fibs in the spanish press...
Spanish authorities admitted Thursday they were contacted about a potential summer attack on civilians in Barcelona but dispute the authenticity of an apparent leaked US intelligence document published in the Spanish media.TrendsCatalonia terror attacks
No hemos recibido nada de la CIA y nosotros, como dice el periodico, también protegeremos a las fuentes policiales
— Mossos (@mossos) August 31, 2017In the immediate aftermath of the Las Ramblas attack on August 17 when Younes Abouyaaqoub drove a white van into crowds of civilians, killing 14 people and injuring more than 100, the Spanish newspaper El Periodicoclaimed that authorities had ignored warnings of an impending attack from as far back as May.
El aviso de la CIA a los @mossos y otras claves del día, en un minuto https://t.co/VJnrotAI1O#FelizJueves
— El Periódico (@elperiodico) August 31, 2017On Thursday, the news agency doubled down on its claim, publishing what it purports to be a document from the National Counterterrorism Center (NCTC) which coordinates the efforts of the CIA, the NSA and the FBI, among others.
However, many dispute its authenticity, citing major discrepancies in the specific language used in the alleged intelligence document, among other notable flaws.
Julian Assange and WikiLeaks weighed in on the debate, pointing out several mistakes in the style of writing, including: the use of the Spanish spelling 'Irak' instead of 'Iraq,' the Spanish word 'nota' rather than the English 'notice.’
#Catalonia attackers avoided checks designed for detecting terror threats – Spanish ministerhttps://t.co/mDHg0dv6k4pic.twitter.com/HbOgUaE3t5
— RT (@RT_com) August 28, 2017Another notable feature pointed out was the use of Spanish-style quotation marks ‘<<’ as opposed to inverted commas typically used in English.
Assange even called for El Periodico’s editor to resign, claiming it was a deliberate attempt to mislead the public.
The editor of El Periódico, @Enric_Hernandez, should resign. He has engaged in a clear attempt to mislead the public. #lacia#elperiodico
— Julian Assangethe masters of the game...
Although the principle of state sovereignty lies at the heart of international law, the super powers have not refrained from corrupting governments, destabilising societies, eliminating their leaders and even overthrowing regimes by means of covert action. While this form of interference is relatively inexpensive when weighed against the potential gains, it inevitably undermines trust among nations.
The Anglo-Saxons have become the masters of the game. As joint signatories to a 1948 secret military pact (UK-USA + Canada, Australia, New Zealand), they fashioned espionage and covert action tools to serve their common project: the Cold War. They were rivaling in this field against the Soviet Union, over which they had already attained undeniable superiority. Both Maoist China and post-colonial France also resorted to analogous means with a view to securing zones of interest, mainly in Africa.
The landscape changed completely after the demise of the USSR. China stopped financing armed revolutionary groups all around and concentrated on pragmatic intelligence efforts to sustain economic cooperation development. France withdrew from its private reserve in Africa to leave room for the European Union. Having outlived the Yeltsin abyss, Russian intelligence set about restructuring at the national level and in their historical area of influence (newly independent ex-Soviet states) by mobilizing against external intrusions rather than interfering in the affairs of other countries.
As of 1995, the Anglo-Saxons invested massively in their secret services, whose budget tripled over a 15-year period. In addition, they have drawn the Israeli services into their structure either as full members or as subcontractors. In 2009, the Anglo-Saxon services (except Israel) operate on an employment level of 250,000 men and a budget exceeding 100 billion dollars (i.e. 15 times higher than Russia’s, virtually their main competitor). In effect, espionage and covert action have become the essential tools of forced globalisation.
Read more:
http://www.voltairenet.org/mot209.html?lang=en
Read from top.
Read also:
http://www.yourdemocracy.net.au/drupal/node/28605
a double-cross...
REALITY WINNER WAS sentenced today to 63 months in prison for disclosing a top-secret NSA document describing a hacking campaign directed by the Russian military against U.S. voting systems.
On June 5, 2017, The Intercept published a story about the document. We did not know the identity of the source who had sent it to us. Shortly after we posted our story, we learned that Winner had been arrested two days earlier. After an internal review, we acknowledged shortcomings in our handling of the document. However, it soon became clear that the government had at its disposal, and had aggressively used, multiple methods to quickly hunt down Winner.
The information in The Intercept story on the NSA report played a crucial role in alerting local election officials who had been in the dark about the cyberattack — a public service that was implicitly acknowledged in a recent report from the Senate Intelligence Committee. As a former official from the Department of Homeland Security told The Intercept’s Sam Biddle, transmitting word of the cyberattacks down the chain was “not a high priority issue” for the NSA. The vulnerability of the American electoral system is a national topic of immense gravity, but it took Winner’s act of bravery to bring key details of an attempt to compromise the democratic process in 2016 to public attention. Those same details were included in the July indictment of alleged Russian military intelligence operatives issued by Special Counsel Robert Mueller.
Instead of being recognized as a conscience-driven whistleblower whose disclosure helped protect U.S. elections, Winner was prosecuted with vicious resolve by the Justice Department under the Espionage Act. Her plea agreement reflects the conclusion of Winner and her lawyers that the terms of this deal represent the best outcome possible for her in the current environment. She not only faced unrelenting pressure from prosecutors, but a series of setbacks in the courtroom severely restricted her lawyers’ ability to defend her.
The Intercept’s parent company, First Look Media, contributed to Winner’s legal defense through the Press Freedom Defense Fund.
Reality Winner’s courage and sacrifice for the good of her country should be honored, not punished. Selective and politically motivated prosecutions of leakers and whistleblowers under the Espionage Act — which dramatically escalated under Barack Obama, opening the door for the Trump Justice Department’s abuses — are an attack on the First Amendment that will one day be judged harshly by history.
Read more:
https://theintercept.com/2018/08/23/reality-winner-sentenced-nsa-russia-...
----------------
The document analysis says:
While the document provides a rare window into the NSA’s understanding of the mechanics of Russian hacking, it does not show the underlying “raw” intelligence on which the analysis is based. A U.S. intelligence officer who declined to be identified cautioned against drawing too big a conclusion from the document because a single analysis is not necessarily definitive.
--------------------
Gus: there is something called disinformation and double-cross. Most spy agency are expert at both. It is the first occupation of all "intelligence" spy agencies: the fabrication of fake documents. Such secret documents as those passed on by Winner to the Intercept, are thus often fake. What is the purpose of these "fakes"? First some are planted to weed out "whistleblowers" or spies. Second, most are worded to implicate "the enemy" and boost patriotism. Third some are politically motivated to boost the credibility of one side over another. Fourth, they are created to deceive the enemy (All this in which ever order of importance to suit the situation).
--------------------
So upon receipt of "the document", The Intercept HAD TO EDITORIALISE THAT:
This NSA summary judgment is sharply at odds with Russian President Vladimir Putin’s denial last week that Russia had interfered in foreign elections: “We never engaged in that on a state level, and have no intention of doing so.” Putin, who had previously issued blanket denials that any such Russian meddling occurred, for the first time floated the possibility that freelance Russian hackers with “patriotic leanings” may have been responsible. The NSA report, on the contrary, displays no doubt that the cyber assault was carried out by the GRU.
IF YOU DON'T UNDERSTAND WHAT THIS MEANS TAKE A BATH.
"it does not show the underlying “raw” intelligence on which the analysis is based." is as weak as piss... Without raw data and original evidence, no such documents are credible. This is why Wikileaks only publish ORIGINALS not assessments.
Winner should not be in prison. I often refer to the intelligence on Saddam's WMDs having been "fabricated". And we know it was. But this WAS NOT NEW. Since about 600 BC, the fabrication of fake documentation has been a way to write favourable history. Christianity is based on such documentation. Islam is the same. The US hegemony is based on such fabrication. It's very sophisticated deceit, but deceit it is. Read from top.
Read also:
on military "intelligence"...
throwing sand in their face since 1917...
the empire's liberal-progressives-neocons want war as they fear the truth more than bombs...
the aim of the game is to hate russia more than anything...
we need him more than ever...
under the surface of news — more on the momentous 2, February 1959, leading eventually to brexit...
agencies keeping us in the dark...
the news — february 2, 1959... regard yourselves, gentlemen, as victors in this war...
of lies, porkies and deceit...and many more articles on this site on this very subject...
Read from top.